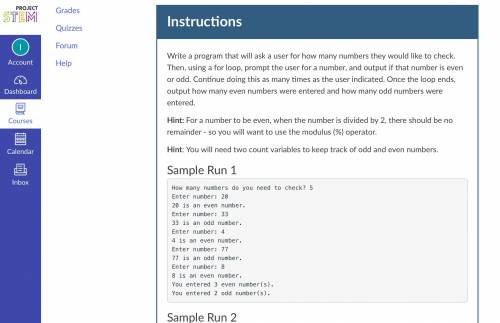
Please help this is assignment 4 on project stem
...

Computers and Technology, 18.12.2021 21:30 black99girl
Please help this is assignment 4 on project stem

Answers: 1
Another question on Computers and Technology

Computers and Technology, 22.06.2019 12:50
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks.requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1

Computers and Technology, 23.06.2019 00:20
Ihave been given the number of guns per 100, and the total firearm-related deaths per 100,000. i have to find the actual number of guns per country and actual number of gun-related deaths. if somebody could show me how to do 1 question, i can finish the rest, i am just confused. tia
Answers: 3

Computers and Technology, 23.06.2019 04:31
Q13 what function does a security certificate perform? a. creates user accounts b. scrambles data c. identifies users d. creates password policies e. provides file access
Answers: 1

Computers and Technology, 24.06.2019 16:30
What is the item which could be matched with a statement below? software installed on a computer that produces pop-up ads using your browser an example of social engineering malware loads itself before the os boot is complete type of spyware that tracks your keystrokes, including passwords windows key + l the practice of tricking people into giving out private information or allowing unsafe programs into the network or computer when someone who is unauthorized follows the employee through a secured entrance to a room or building a type of malware that tricks you into opening it by substituting itself for a legitimate program a computer that has been hacked, and the hacker is using the computer to run repetitive software in the background without the user's knowledge an infestation designed to copy itself repeatedly to memory, on drive space, or on a network
Answers: 1
You know the right answer?
Questions

Mathematics, 13.01.2021 22:00


Mathematics, 13.01.2021 22:00

Arts, 13.01.2021 22:00


Mathematics, 13.01.2021 22:00



Mathematics, 13.01.2021 22:00

Chemistry, 13.01.2021 22:00

Mathematics, 13.01.2021 22:00


Mathematics, 13.01.2021 22:00

History, 13.01.2021 22:00

Mathematics, 13.01.2021 22:00

Mathematics, 13.01.2021 22:00


Mathematics, 13.01.2021 22:00

English, 13.01.2021 22:00

Chemistry, 13.01.2021 22:00



