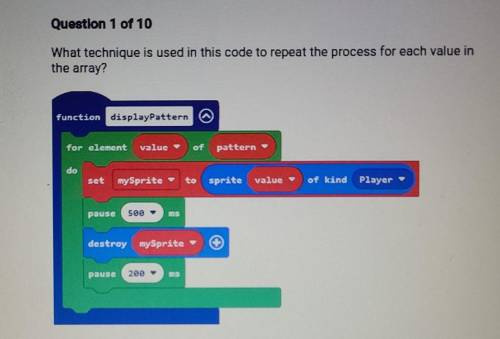
What technique is used in this code to repeat the process for each value in the array?
a....

Computers and Technology, 27.10.2021 06:10 reneewilliams20
What technique is used in this code to repeat the process for each value in the array?
a. pause blocks
b. a repeat loop
c. a for loop
d. an array block

Answers: 1
Another question on Computers and Technology

Computers and Technology, 23.06.2019 09:30
You have been supporting csm tech publishing's windows server 2016 server network for over a year. the office has two windows server 2016 servers running active directory and a number of other roles. management has informed you that a small sales office is opening in the same building three floors up. the sales manager wants to install a sales application on a server located in the sales office. this server will have limited physical security because there's no special room dedicated for it, which means it will be accessible to non-it personnel and visitors. you're considering installing windows server 2016 server core on the new server because accessing its console regularly probably won't be necessary, and this server will be managed from one of the other csm tech publishing servers. what are the benefits and drawbacks of using server core for this branch office? what are some things you should do to set up this server management environment?
Answers: 1

Computers and Technology, 23.06.2019 17:00
What are the 12 colors of the spectrum called?
Answers: 1

Computers and Technology, 24.06.2019 16:30
What is the item which could be matched with a statement below? software installed on a computer that produces pop-up ads using your browser an example of social engineering malware loads itself before the os boot is complete type of spyware that tracks your keystrokes, including passwords windows key + l the practice of tricking people into giving out private information or allowing unsafe programs into the network or computer when someone who is unauthorized follows the employee through a secured entrance to a room or building a type of malware that tricks you into opening it by substituting itself for a legitimate program a computer that has been hacked, and the hacker is using the computer to run repetitive software in the background without the user's knowledge an infestation designed to copy itself repeatedly to memory, on drive space, or on a network
Answers: 1

Computers and Technology, 24.06.2019 20:00
Avirus enters a computer or network as code embedded in other software directly from another computer
Answers: 1
You know the right answer?
Questions


Geography, 25.07.2019 01:20

Geography, 25.07.2019 01:20













Mathematics, 25.07.2019 01:30






