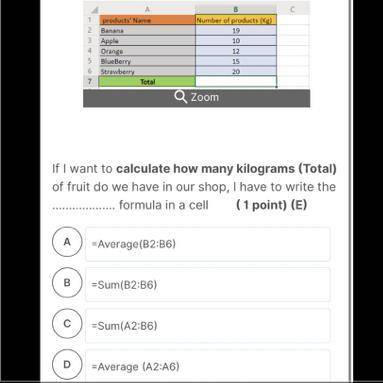
Which one is correct?
...

Answers: 3
Another question on Computers and Technology

Computers and Technology, 21.06.2019 21:00
In this lab, you add a loop and the statements that make up the loop body to a c++ program that is provided. when completed, the program should calculate two totals: the number of left-handed people and the number of right-handed people in your class. your loop should execute until the user enters the character x instead of l for left-handed or r for right-handed. the inputs for this program are as follows: r, r, r, l, l, l, r, l, r, r, l, x variables have been declared for you, and the input and output statements have been written.
Answers: 3

Computers and Technology, 23.06.2019 12:10
2. fabulously fit offers memberships for$35 per month plus a $50 enrollmentfee. the fitness studio offersmemberships for $40 per month plus a$35 enrollment fee. in how many monthswill the fitness clubs cost the same? what will the cost be?
Answers: 1

Computers and Technology, 24.06.2019 15:20
Local area networks use many of the same network technologies and the internet, only on a smaller scale. devices that access lans are equipped with a network interface that contains circuitry for wireless or wired connections. devices also have a physical address, in addition to the ip addresses acquired from a dhcp server. the most popular wired technology is . the most popular wireless technology is , which can be configured as a(n) or star topology. setting up a lan and configuring its router is fairly easy. the first step is to change the standard to one that is secure. next, create a(n) that uniquely identifies the network by name. it is also important to activate wireless to prevent wireless signals from being intercepted during transmission. a limited-access network can be created for visitors to use. by activating , the router will be able to assign ip addresses to each device that joins the network. to connect to a secure lan that is protected by encryption, an encryption , or password, is required. lans can be used to access data collected by iot devices and the networks that tie these devices together. technologies such as rfid, nfc, bluetooth smart, zigbee, and z-wave offer -power links, essential for battery-powered devices that can’t expend excess amounts of energy transmitting data.
Answers: 1

Computers and Technology, 24.06.2019 16:00
"gps interaction and cognitive process" respond to the following: imagine that you have been asked to design a gps product that will have voice recognition and bluetooth capability. discuss and conceptualize a user interaction model. predict two (2) problems that may arise in gps products with voice recognition and bluetooth capability. recommend solutions for each of these issues. attention is one of the six cognition processes. when attention is applied to a design, the goal is to make it easier for the end user to quickly locate where he / she should type information on the computer or mobile device screen. compare and contrast how the google search engine and the microsoft bing search engine employ the attention cognition process. provide your opinion as to which search engine better employs the attention cognition process and explain why.
Answers: 3
You know the right answer?
Questions


Mathematics, 15.01.2021 18:30


History, 15.01.2021 18:30

Social Studies, 15.01.2021 18:30

Physics, 15.01.2021 18:30

Mathematics, 15.01.2021 18:30

Chemistry, 15.01.2021 18:30

Mathematics, 15.01.2021 18:30




Mathematics, 15.01.2021 18:30

Arts, 15.01.2021 18:30

Mathematics, 15.01.2021 18:30

Mathematics, 15.01.2021 18:30

English, 15.01.2021 18:30



Mathematics, 15.01.2021 18:30