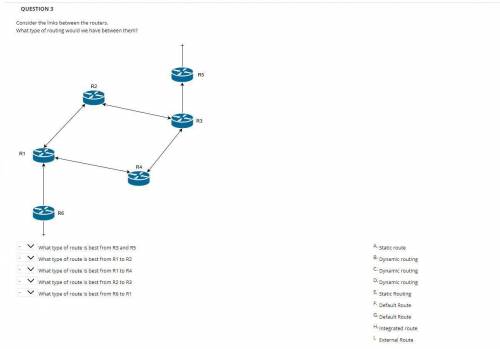
Computer science - Computer Networks -routers
...

Answers: 3
Another question on Computers and Technology

Computers and Technology, 23.06.2019 01:10
Problem 1 - hashing we would like to use initials to locate an individual. for instance, mel should locate the person mark e. lehr. note: this is all upper case. generate a hash function for the above using the numbers on your telephone. you know, each letter has a number associated with it, so examine your telephone keypad. generate 512 random 3 letter initials and take statistics on a linked list array size 512 to hold this information report how many have no elements, 1 element, 2 elements, does this agree with the hashing statistics distribution?
Answers: 1

Computers and Technology, 23.06.2019 18:40
Johnson enterprises uses a computer to handle its sales invoices. lately, business has been so good that it takes an extra 3 hours per night, plus every third saturday, to keep up with the volume of sales invoices. management is considering updating its computer with a faster model that would eliminate all of the overtime processing.
Answers: 2

Computers and Technology, 24.06.2019 00:30
Asecurity policy is a a. set of guidlines b. set of transmission protocols c. written document d. set of rules based on standards and guidelines
Answers: 2

Computers and Technology, 24.06.2019 03:30
The footer area of a web page generally houses which website feature? terms of use web page content business name or title menu headings
Answers: 1
You know the right answer?
Questions




Health, 04.11.2020 18:30






Mathematics, 04.11.2020 18:30

History, 04.11.2020 18:30


Mathematics, 04.11.2020 18:30


Mathematics, 04.11.2020 18:30


Mathematics, 04.11.2020 18:30


Mathematics, 04.11.2020 18:30

History, 04.11.2020 18:30