
Computers and Technology, 01.05.2021 09:10 adelawilliams60
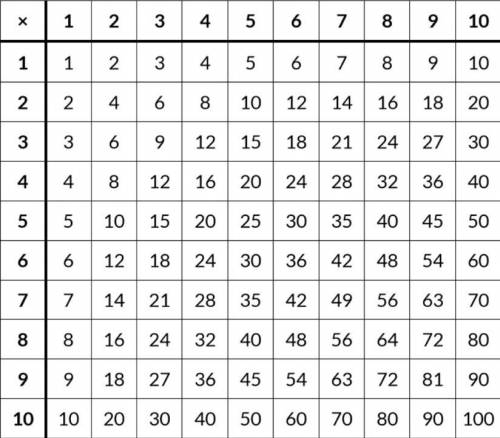
Python - Write a program to print the multiplication table as shown in the image by using for loops.

Answers: 2
Another question on Computers and Technology

Computers and Technology, 21.06.2019 21:30
Asuccessful format string attack attempted to steal user account information by reading from unauthorized memory. answer the followings with proper explanation a)this attack will lead to violation of which security policies?
Answers: 2

Computers and Technology, 22.06.2019 09:50
Assume that you have an sorted array of records. assume that the length of the array (n) is known. give two different methods to search for a specific value in this array. you can use english or pseudo-code for your algorithm. what is the time complexity for each algorithm and why?
Answers: 1

Computers and Technology, 23.06.2019 08:00
The managing director of a company sends a christmas greeting to all his employees through the company email. which type of network does he use? he uses an .
Answers: 3

Computers and Technology, 25.06.2019 08:30
While using pert (program evaluation review technique) and cpm (critical path method) techniques, activities that are not on the critical path are more inflexible than those activities on the critical path. select one: true false
Answers: 1
You know the right answer?
Python - Write a program to print the multiplication table as shown in the image by using for loops....
Questions


English, 25.10.2019 22:43



Mathematics, 25.10.2019 22:43







Biology, 25.10.2019 22:43


Computers and Technology, 25.10.2019 22:43

English, 25.10.2019 22:43

Biology, 25.10.2019 22:43

Mathematics, 25.10.2019 22:43



History, 25.10.2019 22:43



