Computers and Technology, 08.02.2021 19:10 kileylynn
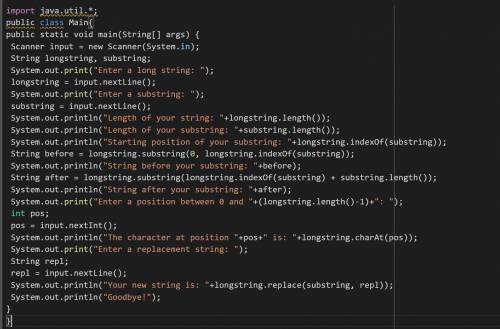
Your goal is to write a JAVA program that will ask the user for a long string and then a substring of that long string. The program then will report information on the long string and the substring. Finally it will prompt the user for a replacement string and show what the long string would be with the substring replaced by the replacement string. Each of the lines below can be produced by using one or more String methods - look to the String method slides on the course website to help you with this project.
A few sample transcripts of your code at work are below - remember that your code should end with a newline as in the textbook examples and should produce these transcripts exactly if given the same input. Portions in bold indicate where the user has input a value.
One run of your program might look like this:
Enter a long string: The quick brown fox jumped over the lazy dog
Enter a substring: jumped
Length of your string: 44
Length of your substring: 6
Starting position of your substring: 20
String before your substring: The quick brown fox
String after your substring: over the lazy dog
Enter a position between 0 and 43: 18
The character at position 18 is x
Enter a replacement string: leaped
Your new string is: The quick brown fox leaped over the lazy dog
Goodbye!
A second run with different user input might look like this:
Enter a long string: Friends, Romans, countrymen, lend me your ears
Enter a substring: try
Length of your string: 46
Length of your substring: 3
Starting position of your substring: 21
String before your substring: Friends, Romans, coun
String after your substring: men, lend me your ears
Enter a position between 0 and 45: 21
The character at position 21 is t
Enter a replacement string: catch
Your new string is: Friends, Romans, councatchmen, lend me your ears
Goodbye!

Answers: 3
Another question on Computers and Technology

Computers and Technology, 21.06.2019 22:00
Which one of the following would administrators use to connect to a remote server securely for administration? a. telnetb. secure file transfer protocol (sftp)c. secure copy (scp)d. secure shell (ssh)
Answers: 1

Computers and Technology, 23.06.2019 17:00
Companies that implement and apply an information system effectively can create
Answers: 1

Computers and Technology, 23.06.2019 22:30
Janice usually works on a particular workbook that contains all business related data. she decides to keep a backup of all the data in a separate workbook. she opens a new workbook to transfer the data. which option should she use to copy all the data from one workbook to another workbook?
Answers: 1

Computers and Technology, 24.06.2019 09:10
to change the number of rows and columns displayed by the excel object a. select the object and drag a size handle on the active object. b. deselect the object and drag a size handle of the object. c. deselect the object and drag a row or column divider of the object. d. select the object and drag a row or column divider on the active object.
Answers: 2
You know the right answer?
Your goal is to write a JAVA program that will ask the user for a long string and then a substring o...
Questions




Mathematics, 23.12.2019 13:31


English, 23.12.2019 13:31


History, 23.12.2019 13:31

Chemistry, 23.12.2019 13:31

Mathematics, 23.12.2019 13:31


History, 23.12.2019 13:31

SAT, 23.12.2019 13:31



Mathematics, 23.12.2019 13:31


Mathematics, 23.12.2019 13:31

Chemistry, 23.12.2019 13:31

History, 23.12.2019 13:31