
Computers and Technology, 01.04.2020 03:14 deisyy101
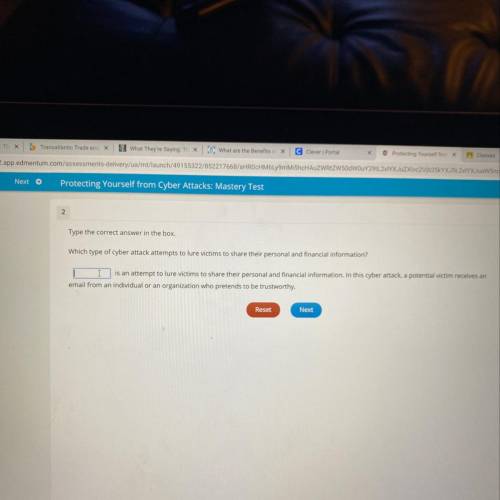
Which type of cyber attack attempts to lure victims to share their personal and financial information?

Answers: 3
Another question on Computers and Technology

Computers and Technology, 22.06.2019 19:00
Which parts of a presentation should be the most general? a. introduction and conclusion b. introduction and outline c. outline and conclusion d. outline and body
Answers: 1

Computers and Technology, 23.06.2019 04:00
Write a method that takes in an array of point2d objects, and then analyzes the dataset to find points that are close together. be sure to review the point2d api. in your method, if the distance between any pair of points is less than 10, display the distance and the (x,y)s of each point. for example, "the distance between (3,5) and (8,9) is 6.40312." the complete api for the point2d adt may be viewed at ~pf/sedgewick-wayne/algs4/documentation/point2d.html (links to an external site.)links to an external site.. try to write your program directly from the api - do not review the adt's source code.
Answers: 1

Computers and Technology, 23.06.2019 07:30
What key should you press and hold to select and open multiple files at one time? enter alt control esc
Answers: 1

Computers and Technology, 23.06.2019 11:00
Describe three characteristics of at-risk drivers. a. b. c. describe three characteristics of safe drivers. a. b. c. describe three driver errors that could cause a collision. a. b. c. how will this information affect you as a driver now and in the future? (2-3 sentences)
Answers: 2
You know the right answer?
Which type of cyber attack attempts to lure victims to share their personal and financial informatio...
Questions







Computers and Technology, 17.09.2019 19:00


Mathematics, 17.09.2019 19:00

Mathematics, 17.09.2019 19:00



Mathematics, 17.09.2019 19:00


Mathematics, 17.09.2019 19:00







