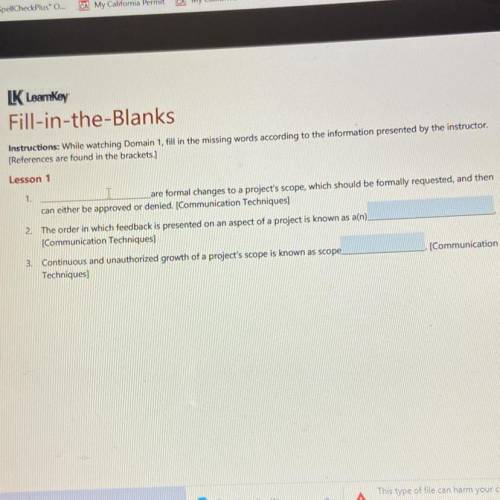
Can someone help me this is for adobe !
...

Answers: 1
Another question on Computers and Technology

Computers and Technology, 21.06.2019 21:30
Asuccessful format string attack attempted to steal user account information by reading from unauthorized memory. answer the followings with proper explanation a)this attack will lead to violation of which security policies?
Answers: 2

Computers and Technology, 22.06.2019 11:00
When working with a team you should always do the following, except? question 3 options: be dependable and trustworthy be sensitive to others feelings do your fair share critique members of the group
Answers: 2

Computers and Technology, 22.06.2019 18:30
Which of these options are the correct sequence of actions for content to be copied and pasted? select content, click the copy button, click the paste button, and move the insertion point to where the content needs to be inserted. click the copy button, select the content, move the insertion point to where the content needs to be inserted, and click the paste button. select the content, click the copy button, move the insertion point to where the content needs to be inserted, and click the paste button. select the content, move the insertion point to where the content needs to be inserted, click the copy button, and click the paste button.
Answers: 3

You know the right answer?
Questions


Mathematics, 25.04.2020 23:50

English, 25.04.2020 23:50





Health, 25.04.2020 23:50

Mathematics, 25.04.2020 23:50

Social Studies, 25.04.2020 23:50

History, 25.04.2020 23:50

Biology, 25.04.2020 23:50

Chemistry, 25.04.2020 23:50


Physics, 25.04.2020 23:50


Mathematics, 25.04.2020 23:51

Biology, 25.04.2020 23:51


Mathematics, 25.04.2020 23:51